When a cybersecurity incident strikes, the technical breach is only half the battle. The other half—often more damaging to long-term business health—is how you communicate about it. We’ve watched organizations with robust security infrastructure crumble under the weight of poor crisis communication, while others with less sophisticated defenses preserved stakeholder trust through transparent, coordinated messaging. The gap between what security teams know and what communications professionals can effectively convey to diverse audiences has become a critical vulnerability in itself. Bridging this divide isn’t optional anymore; it’s a business imperative that determines whether an incident becomes a manageable event or a reputation-destroying crisis.
Building a Cross-Functional Response Framework That Holds Under Fire
The most common failure I see in incident response isn’t technical—it’s organizational. Companies invest millions in security tools but leave communication protocols to chance, assuming teams will naturally coordinate when pressure hits. They won’t.
A functional incident response communication plan starts with documented roles and clear decision-making authority. Your playbook should specify exactly who notifies whom, in what sequence, and with what information at each stage of an incident. This isn’t bureaucracy; it’s precision under chaos. According to cybersecurity communication best practices, prioritizing communication topics such as regulatory compliance and disaster recovery while grounding all messages in facts builds the trust you’ll desperately need when systems are down and stakeholders are demanding answers.
The team composition matters more than most executives realize. Your incident response communication group must include IT security, legal counsel, public relations, human resources, compliance officers, and executive leadership—not as occasional consultants, but as core members with defined responsibilities. Legal needs to understand notification requirements across jurisdictions. PR must craft external messages that satisfy regulatory obligations without creating unnecessary alarm. HR handles internal communication to prevent rumor mills from undermining your official narrative. Each function brings specialized knowledge that prevents costly missteps.
Approval workflows deserve particular attention because they’re where most plans break down. You need escalation paths that prevent delays without sacrificing accuracy. I recommend a tiered approach: pre-approved message templates for common scenarios that communications can deploy immediately, a rapid-response team with authority to approve modifications within defined parameters, and executive sign-off reserved only for major deviations or high-impact communications. Security experts emphasize that confusion during breaches amplifies damage, making tested communication playbooks necessary to prevent conflicting messages and dangerous delays.
Tabletop exercises separate theoretical plans from operational reality. Run these simulations quarterly at minimum, involving every function that would participate in an actual incident. Design scenarios that stress-test your communication protocols: What happens when your primary communication platform is compromised? How do you coordinate messaging across time zones when the incident unfolds at 2 AM? Who has authority to speak to media when the CEO is unreachable? Research on incident response communication shows that incorporating communication response into Business Continuity Plans and running realistic scenario rehearsals significantly improves performance during actual incidents.
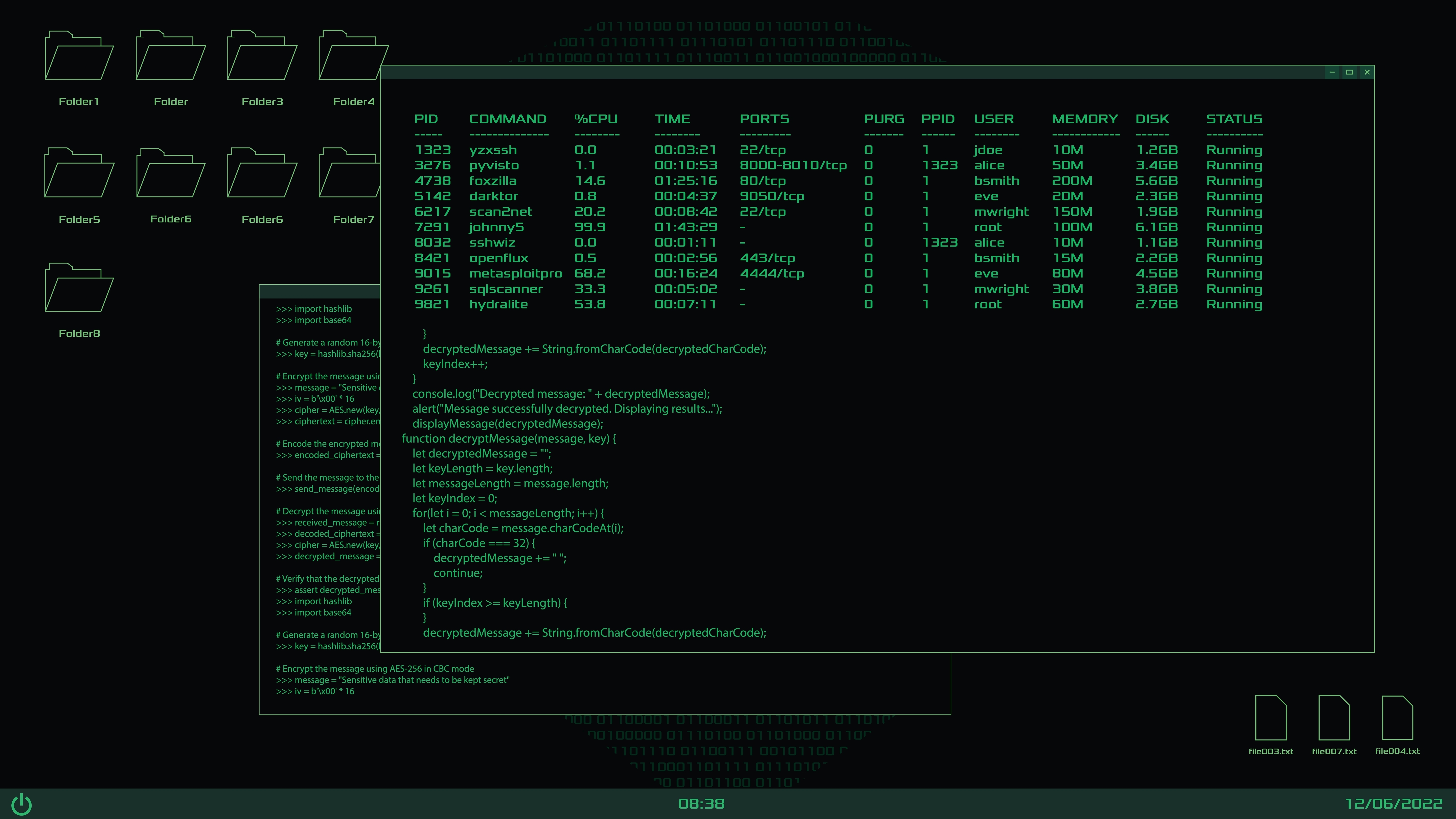
The technical infrastructure supporting your communication during a breach requires as much attention as your security stack. When your network is compromised, you can’t rely on standard email or collaboration tools. Establish encrypted communication platforms with role-based access controls specifically for crisis response. Ensure key personnel can access these systems from personal devices if corporate infrastructure is unavailable. Test these backup channels regularly—discovering they don’t work during an actual incident is not an option.
Translating Technical Risk Into Business Language
The translation problem between security and business functions creates more organizational friction than almost any other communication challenge. Security professionals speak in CVE numbers, attack vectors, and vulnerability scores. Executives think in revenue impact, customer retention, and regulatory exposure. Your job is to be the interpreter.
Start by converting technical vulnerabilities into financial impact statements. When security identifies a critical flaw, don’t present it as “a remote code execution vulnerability in the application layer.” Present it as “a security gap that could allow unauthorized access to customer payment data, potentially exposing us to $4.2 million in regulatory fines under current breach notification laws, plus estimated customer remediation costs of $180 per affected account.” Effective cybersecurity messaging requires describing threats, their potential impact, and relevance in accessible terms that avoid creating unnecessary fear while maintaining transparency.
Create a standard framework for risk communication that includes probability, impact, and mitigation cost. Board members and C-suite executives respond to this structure because it mirrors how they evaluate other business risks. A high-probability, high-impact vulnerability with a low mitigation cost becomes an obvious priority. A low-probability, moderate-impact issue with expensive remediation might be an acceptable risk to manage rather than eliminate. This framework gives leadership the information they need to make informed decisions rather than reacting emotionally to technical jargon they don’t fully understand.
Develop before-and-after messaging templates that demonstrate the translation in action. For example, instead of “We’ve identified a SQL injection vulnerability in the customer portal,” use “Our security team discovered a weakness that could potentially allow unauthorized database access. We’ve already deployed a fix, and our monitoring shows no evidence this weakness was exploited. Customer data remains secure.” The second version conveys the same information but frames it in terms of customer impact and reassurance rather than technical mechanics.
Messaging strategies that maximize engagement with security leadership emphasize crafting narratives that align with business priorities by translating technical challenges into business-relevant terms. This approach helps bridge the gap between security teams who understand the technical details and executives who need to understand business implications.
Establishing Proactive Communication Cadences
Waiting until a crisis to establish communication patterns between security and business leadership is like waiting until a fire to install smoke detectors. The relationships, trust, and shared vocabulary you need during an incident must be built during peacetime.
Institute regular security briefings to the C-suite and board—monthly for executives, quarterly for board members at minimum. These sessions should balance technical detail with business relevance. I recommend a standard agenda: current threat environment relevant to your industry, status of major security initiatives, metrics showing security posture trends, and any emerging risks requiring leadership decisions. Keep these sessions to 30-45 minutes with pre-distributed materials for those who want deeper technical detail.
The metrics you present in these briefings matter enormously. Security teams often default to technical measures like patch compliance rates or vulnerability counts. Business leaders need different indicators: mean time to detect and respond to incidents, percentage of critical assets with current security assessments, compliance status with regulatory requirements, and security investment as a percentage of IT budget compared to industry benchmarks. These metrics connect security activities to business outcomes in ways executives can evaluate and compare.
Internal communication plays a vital role in bridging IT and business functions, ensuring cyber safety messages reach employees effectively through multiple channels and dedicated information hubs. This consistent communication builds the foundation for rapid coordination when incidents occur.
Create a business-IT steering committee with authority to make fast decisions on security matters that affect business operations. This group should meet bi-weekly and include representatives from security, IT operations, key business units, legal, and communications. The committee reviews security initiatives that require business input, resolves conflicts between security requirements and business needs, and serves as a rapid decision-making body during incidents. When crisis hits, this group already has established working relationships and decision-making protocols.
Automate routine security reporting wherever possible. Leadership doesn’t need manual reports on standard metrics—they need dashboards that show security posture at a glance and alert them to anomalies requiring attention. This automation frees security teams to focus on analysis and strategy while keeping business leaders informed without overwhelming them with data.
Protecting Reputation Through Transparent Crisis Messaging
The instinct during a breach is to minimize, delay, and control information. This instinct is almost always wrong. Stakeholders—customers, regulators, employees, partners—will find out about significant incidents. The question isn’t whether they’ll know, but whether they’ll hear it from you first, presented honestly, or discover it through leaks and speculation that destroy trust.
Transparency doesn’t mean sharing every technical detail as you learn it. It means being honest about what you know, what you don’t know yet, and what you’re doing to address the situation. Research on effective communications after cyber incidents demonstrates that clear, simple messaging without jargon, delivered by senior leaders, demonstrates seriousness and helps rebuild trust.
Develop customer notification templates that comply with regulatory requirements while being genuinely helpful to affected individuals. These templates should explain what happened in plain language, what information was potentially accessed, what you’re doing to address the breach, what customers should do to protect themselves, and how they can get more information or assistance. Avoid legal language that obscures meaning—customers facing potential identity theft don’t care about your liability limitations; they care about protecting themselves.
Your media response strategy requires different messages for different breach scenarios. A ransomware attack that disrupts operations but doesn’t compromise customer data requires different talking points than a data breach exposing personal information. Prepare core messages for common scenarios, but recognize that each incident will require customization. Designate trained spokespeople who can stay on message under pressure and know when to say “We don’t have that information yet” rather than speculating.
Employee communication during incidents is often overlooked but critically important. Your staff will hear about breaches—from customers, from media, from their own observations of unusual activity. If they don’t hear the official story from you first, they’ll fill the vacuum with speculation that undermines your external messaging. Communication strategies for cybersecurity emphasize that regular, authentic communication from executives and IT teams builds a security culture that supports coordinated response during crises.
Post-incident communication strategy determines whether you emerge from a breach with damaged or strengthened stakeholder relationships. After immediate crisis response, shift to rebuilding confidence through transparency about what you learned, what you’ve changed, and how you’re preventing recurrence. This might include publishing post-mortem reports, announcing new security investments, or obtaining third-party security certifications. The goal is demonstrating that the incident made you stronger, not just returning to the status quo.
Positioning Your Organization as Security-Conscious
Proactive security storytelling builds the reputation capital you’ll need if an incident occurs. Organizations that communicate regularly about their security investments, certifications, and practices have stakeholder trust to draw on when problems arise. Those that stay silent about security until forced to discuss a breach start from a deficit.
Thought leadership in security doesn’t require disclosing vulnerabilities or sensitive details. It means sharing your approach to security challenges common across your industry, explaining how you think about balancing security with business needs, and demonstrating expertise through content that helps your stakeholders understand the threat environment. Proactive security storytelling and transparent communications build trust and support credibility during crises by establishing consistent messaging across channels.
Transparency reports, published annually or semi-annually, show security maturity without compromising operational details. These reports might include: number and types of security incidents detected and resolved, investments in security infrastructure and training, compliance certifications achieved, results of third-party security audits, and your approach to emerging threats. This transparency demonstrates confidence in your security posture and gives stakeholders concrete evidence of your commitment.
Media relations for cybersecurity topics requires a different approach than traditional PR. Security journalists and industry analysts evaluate claims skeptically and value technical credibility. Build relationships with these influencers before you need them during a crisis. Offer expert commentary on industry security trends, participate in security conferences, and engage authentically with security communities. Messaging that maximizes engagement with security leadership includes engaging industry analysts and using targeted campaigns to shape perception as a security leader through continuous refinement based on feedback.
Content demonstrating security maturity takes many forms: whitepapers explaining your security architecture, case studies showing how you’ve protected customer data, videos of your security operations center (within appropriate boundaries), and certifications like SOC 2, ISO 27001, or industry-specific security standards. This content serves multiple audiences—customers evaluating your trustworthiness, partners assessing risk, and regulators reviewing compliance.
The intersection of corporate communications and cybersecurity messaging isn’t a theoretical exercise—it’s where reputation is built or destroyed, where regulatory compliance succeeds or fails, and where stakeholder trust is earned or lost. The organizations that master this intersection treat communication as a core component of their security program, not an afterthought. They build cross-functional teams that can coordinate under pressure, translate technical risks into business language, maintain regular communication cadences that build trust before crises hit, and balance transparency with strategic messaging during incidents. Start by assessing your current communication protocols against the framework outlined here. Identify the gaps—whether in team structure, message translation, proactive cadences, or crisis playbooks—and address them systematically. The next breach is coming; the question is whether your communication strategy will make it manageable or catastrophic.